
Zero-Day Threat Detection: Why Signatures Are No Longer Enough
Signature-based security tools cannot stop zero-day threats. Learn why behavioral AI has become the essential defense against unknown and novel attack techniques.
Expert threat research, defensive strategies, and industry analysis from the AIFox AI security team.

Signature-based security tools cannot stop zero-day threats. Learn why behavioral AI has become the essential defense against unknown and novel attack techniques.

AI behavioral analysis is redefining how organizations detect and respond to cyber threats. Explore the technology, architecture, and real-world impact of behavioral AI security.

Managing security across AWS, Azure, and GCP creates dangerous visibility gaps. Learn how unified multi-cloud security platforms close those gaps with consistent policy and AI-driven detection.

Security teams are drowning in false positive alerts. Discover how AI-driven correlation and context-aware scoring are finally solving the alert fatigue crisis in enterprise SOCs.

Insider threats are among the hardest security risks to detect. Learn how AI-powered behavioral analytics identifies malicious insider activity without invasive workplace surveillance.
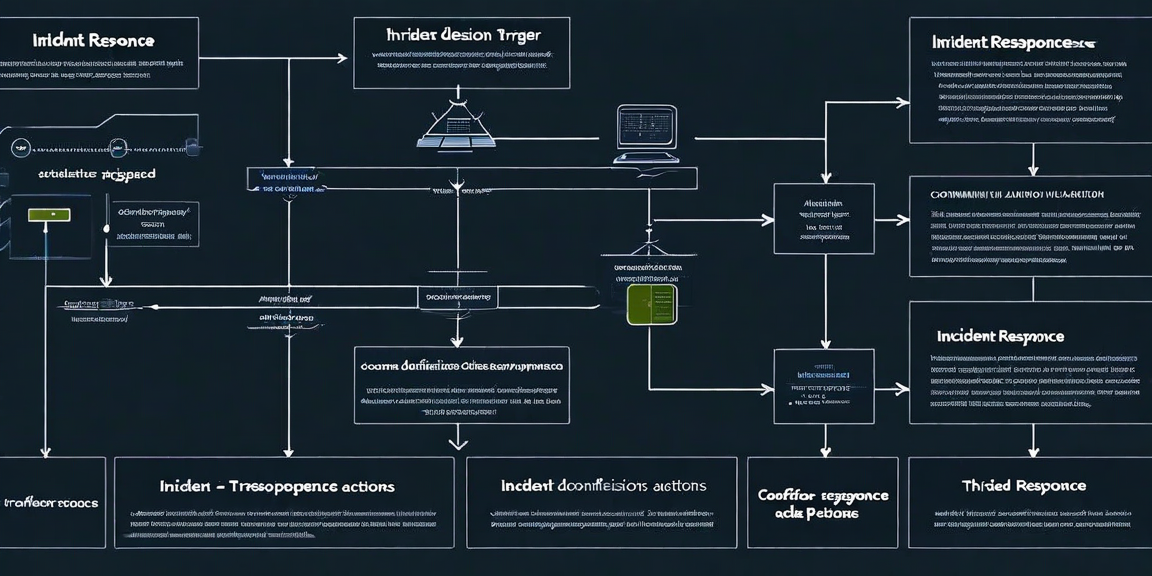
Automated incident response can contain threats in milliseconds — but getting the speed-accuracy balance wrong causes serious harm. This guide explores the trade-offs and how to navigate them.
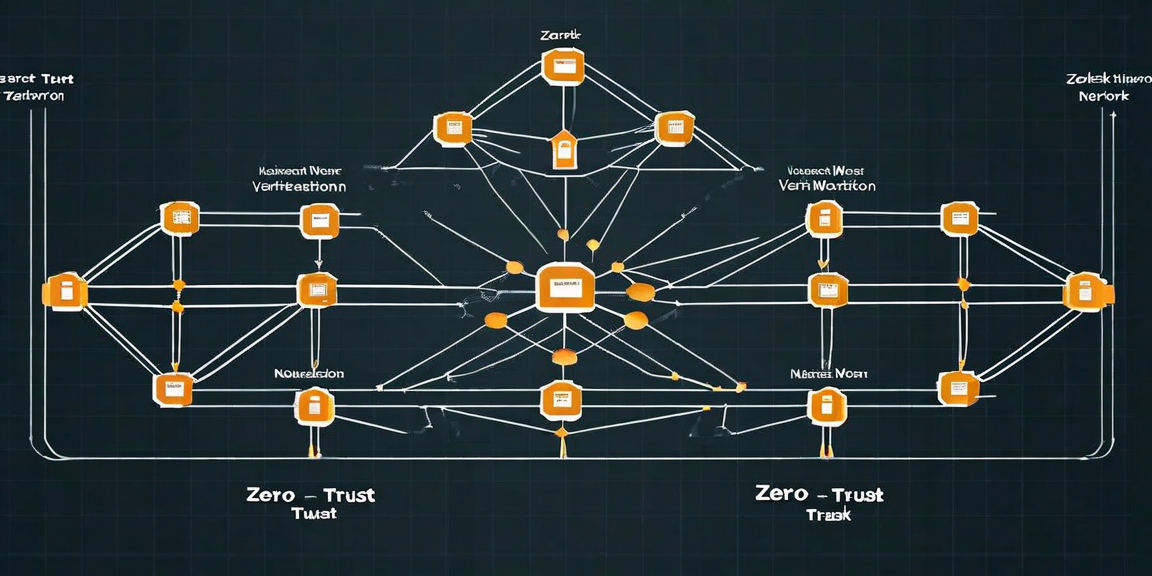
Zero-trust is more than a buzzword — it is a complete rethinking of enterprise security architecture. This practical guide covers how to design and implement zero-trust from the ground up.

Manual compliance audits are costly, stressful, and provide only point-in-time assurance. Learn how compliance automation transforms SOC 2 and ISO 27001 into continuous programs.

Adversarial machine learning techniques are being weaponized to evade AI-powered security systems. Learn how attackers exploit ML weaknesses and how defenders can protect against them.

The modern SOC is neither fully automated nor purely human — it is a collaborative system where AI and analysts each do what they do best. Here is how high-performing SOCs are structuring that collaboration.

Signature-based detection has fundamental limits. Learn how behavioral AI models identify novel attack patterns without prior knowledge of the attack.

A practical guide to structuring AI-driven response playbooks that contain breaches in milliseconds while maintaining meaningful human oversight.

How modern security platforms eliminate the pain of annual SOC 2 audits through continuous evidence collection and automated controls testing.

Analysis of the most common cloud misconfigurations exploited in 2025, how they are introduced, and how automated posture management prevents them.

Step-by-step guidance for enterprise teams migrating from perimeter-based security to a true zero-trust architecture without disrupting operations.

A deep dive into prompt injection, model poisoning, and AI supply chain attacks targeting enterprises that have deployed large language models in production.

With 80% of breaches involving compromised credentials, modern security must treat identity as the primary control plane and apply AI-driven behavioral analytics to detect misuse.

Ransomware groups now exfiltrate data before encrypting it, rendering traditional backup strategies insufficient. Here is how AI-native defenses address modern ransomware tactics.

Industrial control systems were never designed with cybersecurity in mind. This guide covers the unique challenges and modern approaches to securing OT environments.

Insider threats are responsible for 34% of all data breaches. Learn how user and entity behavior analytics identifies malicious insiders before damage is done.

How enterprise security teams build structured threat hunting programs to proactively identify attacker footholds before automated systems flag an alert.

AIFox AI's security research team forecasts the major threat vectors, adversary tactics, and defensive technologies that will define enterprise security in 2025.
Get a personalized threat assessment from our security research team and see AIFox AI in action.